What Are Claude Skills?
Claude Skills are installable knowledge packages that extend Claude's capabilities for specific domains. A skill is a .skill file — a bundled archive containing a SKILL.md instruction file and optional reference materials — that you upload to Claude once and use across all your conversations.
Once installed, a skill activates automatically when your conversation touches its topic area. You don't need to invoke it by name or use special commands. Claude simply becomes a deeper expert in that domain for the duration of your session.
Skills are ideal when you need:
- Consistent, expert-level responses on a specialized topic
- Outputs formatted to professional or regulatory standards (e.g., audit-ready control narratives, policy templates with the right clauses)
- Domain knowledge that goes beyond general LLM training — such as knowing which specific NIST 800-53 controls apply to a given scenario, or which GDPR articles govern international data transfers
How skills work under the hood: Each .skill file contains a primary SKILL.md that is loaded into Claude's context when the skill triggers, plus reference files that are loaded on demand for deeper sub-topics. This "progressive disclosure" pattern keeps context usage efficient while making comprehensive knowledge available when needed.
Who Is This For?
These skills are designed for professionals who work on information security, privacy, and regulatory compliance — whether at organizations seeking certification, development teams building compliant systems, or advisors supporting clients.
Security & Compliance Teams use these skills to accelerate gap assessments, generate first-draft policies, map controls, and prepare evidence packages — compressing weeks of reference work into minutes.
Software Developers & Engineers use them to understand what controls their systems must implement, audit code and architecture for compliance issues, and get actionable technical guidance tied to specific regulatory requirements.
Legal, Privacy & GRC Professionals use them to draft regulatory documents (DPAs, BAAs, privacy notices), answer client questions with precise regulatory citations, and stay current on framework requirements.
Healthcare Organizations use the HIPAA skill to assess systems, generate required notices and agreements, and train staff on obligations — without needing a compliance consultant for every question.
Cloud Service Providers pursuing federal government contracts use the FedRAMP skill to navigate the ATO process, write SSP narratives, manage POA&Ms, and prepare for 3PAO assessments.
Startups and SMBs use these skills to understand what a given framework requires of them, scope their compliance programs, and get expert-quality output without a large in-house team.
The Skills
1. 🔐 ISO 27001
ISO 27001 - Claude Skill/iso27001.skillTurns Claude into an expert ISO 27001 Lead Auditor and ISMS implementation consultant. Covers both ISO 27001:2013 (114 controls, 14 domains) and ISO 27001:2022 (93 controls, 4 themes), defaulting to 2022.
- Runs structured gap analyses against mandatory clauses (4–10) and all Annex A controls
- Generates complete, audit-ready policy documents with document control blocks, scope statements, and clause-to-control mappings
- Builds risk registers and risk treatment plans using the likelihood × impact methodology
- Creates Statement of Applicability (SoA) templates covering all 93 controls
- Guides 2013 → 2022 transition, explaining the 11 new controls and mapping changes
2. ✅ SOC 2
SOC 2 - Claude Skill/soc2.skillTurns Claude into an expert SOC 2 compliance advisor grounded in the AICPA 2017 Trust Services Criteria (TSC) with 2022 Revised Points of Focus. Covers all five TSC: Security (CC1–CC9), Availability (A1), Confidentiality (C1), Processing Integrity (PI1), and Privacy (P1–P8).
- Conducts gap analyses across in-scope TSC criteria with 🔴/🟡/🟢 status ratings and remediation roadmaps
- Drafts all 12 core SOC 2 policies — Information Security, Access Control, Incident Response, Change Management, and more
- Documents controls in auditor-ready format: Control ID, TSC criterion, type, owner, frequency, evidence, and test procedure
- Handles vendor risk: tiering, 32-question security questionnaires, SOC 2 report review, CUEC tracking
3. 🏛️ FedRAMP
FedRamp - Claude Skill/fedramp.skillTurns Claude into a knowledgeable FedRAMP advisor covering the full authorization lifecycle for Cloud Service Providers under NIST SP 800-53 Rev 5. Current as of 2025–2026, incorporating the Rev 5 transition, September 2026 OSCAL mandate, and December 2024 template updates.
- Conducts readiness and gap assessments using a 75+ item checklist across 14 security domains
- Guides authoring of ATO documentation: SSP, POA&Ms, SAPs, SARs, and all required appendices (A–Q)
- Maps NIST 800-53 Rev 5 controls across all 20 control families
- Provides cloud architecture guidance for AWS GovCloud, Azure Government, and Google Cloud Government
- Supports Continuous Monitoring (ConMon) obligations and guides the Rev 4 → Rev 5 transition
4. 🇪🇺 GDPR
GDPR - Claude Skill/gdpr-compliance.skillTurns Claude into an expert GDPR compliance assistant bridging technical and legal perspectives. Covers full EU GDPR with notes on UK GDPR (DPA 2018) where rules differ.
- Audits code, APIs, database schemas, and architectures for GDPR violations with severity-graded findings (🔴/🟡/🟢) mapped to specific GDPR articles
- Drafts compliance documents: Privacy Notices (Art. 13/14), Data Processing Agreements (Art. 28), Cookie/Consent Banners, DPIAs (Art. 35), Data Retention Policies
- Answers compliance questions with authoritative article citations — every response leads with the governing article
- Covers lawful basis, consent, data subject rights (Arts. 15–22), international transfers (Arts. 44–49), breach response (Arts. 32–34)
5. 🏥 HIPAA
HIPAA - Claude Skill/hipaa-compliance.skillTurns Claude into a knowledgeable HIPAA compliance advisor covering the Privacy Rule, Security Rule, and Breach Notification Rule (45 CFR Parts 160 and 164, as amended by HITECH).
- Reviews documents, systems, and architectures for HIPAA compliance with structured findings: CFR citations, risk levels (High / Medium / Low), and remediation steps
- Generates HIPAA-compliant documents from nine ready-to-use templates: NPP, BAA, Authorization Forms, Workforce Training Acknowledgments, Security Incident Reports, Risk Analysis Templates
- Advises on technical safeguards for AWS, Azure, GCP, FHIR APIs, mobile/BYOD, and DevOps — all 54 Security Rule implementation specifications
- Guides breach response using the 4-factor risk assessment, notification timelines, and HHS reporting obligations
6. 🛡️ NIST CSF
NIST Cybersecurity framework - Claude Skill/NIST Cybersecurity.skillTurns Claude into an expert NIST Cybersecurity Framework advisor covering both CSF 2.0 (February 2024) and CSF 1.1 (April 2018), defaulting to CSF 2.0. Covers all six functions — Govern, Identify, Protect, Detect, Respond, Recover — including the new Govern function in CSF 2.0.
- Conducts structured gap assessments across all six CSF 2.0 functions, categories, and subcategories
- Builds Organisational Profiles — Current and Target — aligned to business context and risk tolerance
- Assesses Implementation Tiers (1–4) and provides targeted advancement guidance
- Maps CSF subcategories to NIST SP 800-53, ISO 27001:2022, and CIS Controls v8
- Guides CSF 1.1 → CSF 2.0 migration with a detailed subcategory mapping and migration checklist
7. 💳 PCI DSS
PCI Compliance - Claude Skill/PCI-Compliance.skillTurns Claude into an expert PCI DSS compliance advisor covering PCI DSS v4.0.1 (June 2024 — current), including all requirements that became mandatory on March 31, 2025. Covers all 12 requirements, all 8 SAQ types, merchant and service provider levels, and v4.0 changes from v3.2.1.
- Scopes the Cardholder Data Environment (CDE) — identifies what's in scope, assesses network segmentation, recommends scope reduction via tokenisation or P2PE
- Selects the correct SAQ type — decision tree for SAQ A, A-EP, B, B-IP, C, C-VT, P2PE, and D
- Conducts structured gap assessments across all 12 requirements with QSA evidence requirements
- Guides v3.2.1 → v4.0.1 migration including MFA expansion, payment page script integrity (Req 6.4.3), phishing protection (Req 5.4.1)
8. 🚨 TSA Cybersecurity
TSA Compliance - Claude Skill/TSA-Compliance.skillTurns Claude into an expert TSA cybersecurity directive advisor for critical transportation infrastructure. Covers all current TSA Security Directive series — SD Pipeline-2021-01G, SD Pipeline-2021-02F, SD 1580-21-01E (freight rail), and SD 1582-21-01E (transit/passenger rail) — plus the November 2024 NPRM.
- Determines applicability — which directive series applies to your organisation and what it means for compliance
- Runs structured gap assessments across four technical domains: IT/OT network segmentation, access controls (MFA), continuous monitoring, and patch management
- Drafts CRMP documents: Cybersecurity Implementation Plan (CIP/COIP), IRP, Architecture Design Review (ADR), and Cybersecurity Assessment Plan (CAP)
- Guides OT/ICS-specific implementation — data diodes, jump servers for legacy HMIs, passive monitoring tools (Claroty, Dragos, Nozomi)
9. 🤖 ISO 42001 AI Management System
ISO 42001 - Claude Skill/ISO-42001.skillTurns Claude into an expert ISO/IEC 42001:2023 AI Management System (AIMS) advisor — the world's first international standard for AI governance. Serves both AI providers (organisations developing or deploying AI) and AI users (organisations integrating third-party AI).
- Conducts structured gap assessments across all mandatory clauses (4–10) and all 38 Annex A controls (domains A.2–A.10) with 🔴/🟡/🟢 status and phased remediation roadmap
- Guides the mandatory AI System Impact Assessment (AISIA) — identifying affected populations, assessing impact dimensions, classifying impact level (Low/Medium/High)
- Performs AI risk assessment across model risks, data risks, operational risks, and supply chain risks
- Generates a complete Statement of Applicability (SoA) covering all 38 Annex A controls (A.2.2–A.10.4)
- Maps ISO 42001 to the EU AI Act — aligns AISIA to the Fundamental Rights Impact Assessment (FRIA) for high-risk AI systems
10. 🔒 ISO 27701 Privacy Information Management
ISO 27701 - Claude Skill/iso27701.skillTurns Claude into an expert ISO/IEC 27701:2025 Privacy Information Management System (PIMS) advisor. Covers the full lifecycle from gap assessment through certification for both PII controllers and PII processors, and handles both the new standalone 2025 edition and the legacy 2019 extension edition.
- Conducts structured gap analyses across all mandatory HLS clauses (4–10) and all 78 Annex A controls — 31 for PII controllers (A.1), 18 for PII processors (A.2), 29 shared security controls (A.3)
- Generates complete PIMS policy documents — Privacy Policy, RoPA, Data Subject Rights Procedure, DPAs, Privacy by Design Procedure, and more
- Builds privacy risk registers, triggers DPIAs for high-risk processing, and produces risk treatment plans
- Creates Statements of Applicability (SoA) scoped to the organization's role (controller, processor, or both)
- Guides 2019 → 2025 transitions with full control mapping table and timeline to the October 2028 deadline
- Maps ISO 27701 to GDPR article by article, plus CCPA/CPRA, LGPD, PIPEDA, and UK GDPR
11. 🏦 DORA Digital Operational Resilience
DORA - Claude Skill/dora.skillTurns Claude into an expert advisor on Regulation (EU) 2022/2554 (DORA) — the anchoring ICT regulation for EU financial entities since 17 January 2025. Encodes all 64 DORA articles, all 12 adopted RTS/ITS, and provides precise article-level guidance. Explicitly separates DORA from NIS2, legacy EBA ICT guidelines, and ISO 27001.
- Conducts structured DORA gap analyses across ICT risk management (Chapter II, Art. 5–16), incident management (Chapter III, Art. 17–23), TLPT (Chapter IV, Art. 24–27), and third-party risk (Chapter V, Art. 28–44)
- Guides ICT incident classification against Art. 18 criteria and CDR (EU) 2024/1772 materiality thresholds, with a full decision tree for major vs. non-major
- Builds three-stage reporting procedures per Art. 19: initial (4h), intermediate (72h), final (1 month), including content requirements per CDR (EU) 2025/301
- Reviews contracts against Art. 30(2)(a)–(i) mandatory provisions and flags the audit-rights gap common with hyperscale cloud providers
- Builds and validates the Register of Information with all mandatory fields per CIR (EU) 2024/2956
- Scopes TLPT programmes per Art. 26 and CDR (EU) 2025/1190, covering threat intelligence, red team, mutual recognition, and tester qualifications
12. 🇮🇳 DPDPA India Digital Personal Data Protection
DPDPA - Claude Skill/dpdpa.skillTurns Claude into an expert advisor on India's Digital Personal Data Protection Act, 2023 and the finalized DPDP Rules, 2025 (notified 13 November 2025, effective 13 May 2027). Covers all 44 sections and 23 Rules with section-level citations, GDPR-alignment mapping, and guidance for both Indian companies and global organizations with Indian data subjects.
- Conducts structured DPDPA gap analyses covering notice/consent (Sections 5–6 + Rules 3–4), Data Fiduciary obligations (Section 8 + Rules 6–9), children's data (Section 9 + Rules 10–12), and SDF obligations (Section 10 + Rule 13)
- Distinguishes DPDPA from GDPR across 8 dimensions — digital-only scope, no legitimate interests basis, unconditional consent + no bundling, blacklist cross-border transfers, narrower erasure right, India-resident DPO for SDFs, 18-year children's threshold, single Board enforcement
- Guides breach notification per Section 8(6) and Rule 6 — 72-hour Board notification, all breaches notifiable (no risk threshold), Processor cascade obligations
- Designs children's data programmes — Rule 12 parental verification (DigiLocker, government tokens, virtual tokens) and absolute prohibitions on tracking, profiling, and targeted advertising for under-18s
- Advises Significant Data Fiduciaries on India-resident DPO, annual DPIA, annual independent audit, and data localisation readiness
- Guides Data Principal rights fulfilment — access (Section 11), correction/erasure (Section 12), grievance redressal (Section 13), and the unique right to nominate (Section 14)
13. 🛡️ CMMC 2.0 Cybersecurity Maturity Model Certification
CMMC - Claude Skill/cmmc.skillTurns Claude into an expert CMMC compliance advisor for US defense contractors. Covers all three CMMC levels — Level 1 (17 FAR 52.204-21 practices), Level 2 (110 NIST SP 800-171 Rev 2 practices/C3PAO), and Level 3 (110+ NIST SP 800-172/DIBCAC) — under the final 32 CFR Part 170 rule effective December 16, 2024.
- Determines the correct CMMC level based on FCI vs. CUI handling, DFARS clauses (7012, 7019, 7020, 7021), and program criticality
- Conducts structured gap assessments across all 17 domains — AC, AT, AU, CM, IA, IR, MA, MP, PE, PS, RA, CA, SC, SI — against all 110 Level 2 practices
- Drafts System Security Plans (SSP) covering system boundary, CUI data flows, and implementation narratives for all 110 practices
- Calculates SPRS scores (starting at 110; deductions per unmet practice; range −203 to +110) and prioritises highest-impact gaps
- Manages POA&M lifecycle — identifies allowable vs. blocked practices, drafts milestones, tracks 180-day closure deadline
- Prepares for C3PAO assessments — four-phase process, evidence requirements, critical practices blocking conditional certification
- Explains DFARS obligations: 72-hour DIBNET incident reporting (DFARS 252.204-7012) and subcontractor flow-down (DFARS 252.204-7021)
14. 🤖 NIST AI Risk Management Framework
NIST AI RMF - Claude Skill/nist-ai-rmf.skillTurns Claude into an expert advisor on the NIST AI Risk Management Framework (AI RMF 1.0), published January 2023 as NIST AI 100-1. Covers all four core functions — GOVERN, MAP, MEASURE, MANAGE — their 19 categories and subcategories, the AI RMF Playbook's suggested actions, and deep guidance on AI trustworthiness evaluation.
- Builds AI organizational profiles — Current Profile and Target Profile across all 19 categories with gap scoring and prioritised roadmap
- Conducts GOVERN gap assessments across all 6 categories (GV-1 to GV-6) — AI risk policies, accountability, roles, cross-functional teams, risk tolerance, regulatory alignment
- Guides MAP context-setting for any AI system — intended use, affected stakeholder mapping, risk/benefit analysis, likelihood/impact characterization
- Specifies MEASURE 2.x pre-deployment evaluation — bias/fairness (demographic parity, equalized odds), explainability (SHAP, LIME), adversarial robustness, privacy, human oversight
- Builds AI risk registers with AI RMF category citations (e.g., MAP 5.2, MEASURE 2.2, MANAGE 2.3), trustworthiness property at risk, and treatment options
- Maps AI RMF to ISO 42001, EU AI Act, and NIST CSF — showing which categories satisfy Art. 9, equivalent ISO 42001 clauses, and how AI RMF extends cybersecurity frameworks
15. 🏦 SWIFT Customer Security Programme (CSP)
SWIFT CSP - Claude Skill/swift-csp.skillTurns Claude into an expert advisor on the SWIFT Customer Security Controls Framework (CSCF) v2025 — the mandatory cybersecurity programme for all SWIFT network participants. Covers all 31 controls (23 mandatory + 8 advisory), all five architecture types (A1/A2/A3/A4/B), the KYC-SA annual attestation process, and cross-framework mapping to ISO 27001:2022, PCI DSS v4.0.1, and NIST CSF 2.0.
- Determines the correct SWIFT architecture type (A1/A2/A3/A4/B) and produces the full mandatory/advisory control applicability matrix for your deployment
- Conducts structured CSCF v2025 gap assessments with 🔴/🟡/🟢 status per control, evidence requirements, and prioritised remediation roadmaps
- Provides deep-dive implementation guidance for all 23 mandatory controls — purpose, requirements, implementation steps, and audit evidence artifacts
- Guides the complete KYC-SA attestation process — evidence prep, independent assessor qualification, portal submission, and post-submission counterparty visibility
- Advises on SWIFT-specific incident response — 24-hour initial notification to security@swift.com, 30-day full report, evidence preservation, and Control 7.1 IRP requirements
- Maps CSCF to ISO 27001:2022, PCI DSS v4.0.1, and NIST CSF 2.0 — identifying synergies and SWIFT-specific additions not covered by existing certifications
16. 🇦🇺 Australian Information Security Manual (ISM)
ISM - Claude Skill/ism.skillTurns Claude into an expert advisor on the Australian Information Security Manual (ISM) — the whole-of-government cybersecurity framework published by the Australian Signals Directorate (ASD) for federal and state government entities and their supply chains. Covers all 22 guideline chapters, control applicability markings (NC/OS/PROTECTED/SECRET/TOP SECRET), the IRAP assessment programme, system authorisation, and the Essential Eight relationship.
- Applies the ISM's control applicability marking system — determines NC/OS/PROTECTED/SECRET/TOP SECRET controls for a given system using the stacking rule, and scopes gap analyses accordingly
- Guides the complete system authorisation pathway — six-step cycle (define, select, implement, assess, authorise, monitor), SSP structure, and ATO sign-off by the Authorising Official
- Prepares agencies for IRAP assessments — full artefact checklist, what assessors evaluate, post-assessment POA&M → ATO pathway, and 24-month re-assessment obligations
- Provides deep-dive guidance on all 22 ISM guideline chapters: system hardening (Ch. 13), patch management SLAs (Ch. 14), logging/retention (Ch. 15), cryptography (Ch. 20), email security (Ch. 18), networking (Ch. 19)
- Explains the Essential Eight as a prioritised ISM subset — maps each of the 8 strategies to ISM chapters, covers ML0–ML3 maturity levels, and distinguishes Essential Eight from full ISM compliance
- Advises private sector cloud providers and supply chain partners on ISM obligations under government contracts and when IRAP is required for non-government entities
17. 🇪🇺 EU NIS2 Directive
NIS2 - Claude Skill/nis2.skillTurns Claude into an expert advisor on the EU NIS2 Directive (Directive (EU) 2022/2555) — the EU's overarching cybersecurity framework for essential and important entities, in force since 27 December 2022 (transposition deadline 17 October 2024). Replaces NIS1 with expanded scope, stronger incident reporting, management body accountability, and penalties up to €10M or 2% of global turnover.
- Determines entity classification — Essential Entity (Annex I: 11 highly critical sectors including energy, transport, health, banking) or Important Entity (Annex II: 7 other critical sectors) — with size-threshold analysis to confirm scope
- Guides compliance with all 10 Art. 21 cybersecurity risk management measures: risk analysis policies, incident handling, BCP/DR/crisis management, supply chain security, secure SDLC and vulnerability management, effectiveness assessment, cyber hygiene training, cryptography, HR security and access control, and MFA/secure communications
- Walks through the Art. 23 incident reporting workflow: 24-hour early warning, 72-hour incident notification, and 1-month final report — with content requirements for each stage and significant incident threshold guidance
- Explains Art. 20 governance obligations — management body approval, mandatory cybersecurity training, and personal liability under Member State transposition law
- Performs ISO 27001 gap analysis — maps ISO 27001:2022 Annex A controls to NIS2 Art. 21 measures and identifies critical gaps (Art. 20 governance, Art. 23 reporting timelines, MFA mandate, ENISA supply chain assessments)
- Addresses the DORA lex specialis interaction — explains DORA precedence for financial entities under Art. 4, identifies residual NIS2 obligations, and recommends an integrated compliance programme
18.  CCPA/CPRA California Privacy
CCPA/CPRA California Privacy
CCPA - Claude Skill/ccpa.skill
Turns Claude into an expert advisor on California's comprehensive privacy laws — the California Consumer Privacy Act (CCPA, effective Jan 1, 2020) and the California Privacy Rights Act (CPRA/Proposition 24, effective Jan 1, 2023). CPRA created the California Privacy Protection Agency (CPPA), introduced Sensitive Personal Information (SPI), and added rights to correct PI, limit SPI use, and require data retention disclosures.
- Determines business applicability — whether an organisation meets any of the three CCPA/CPRA thresholds ($25M revenue OR 100K+ consumers/households OR 50%+ revenue from PI sale/sharing) and outlines resulting obligations
- Guides consumer rights fulfillment — step-by-step workflows for right to know, delete, correct, opt-out of sale/sharing, limit SPI use, portability, and non-discrimination — including identity verification, exception handling, response deadlines (45 days / 15 business days for SPI), and service provider propagation
- Classifies ad tech, cookie tracking, and data sharing as "sale" or CPRA "sharing" (cross-context behavioral advertising) and advises on Global Privacy Control (GPC) signal compliance and consent management platform implementation
- Identifies and advises on Sensitive Personal Information (SPI) — precise geolocation, biometrics, health data, SSNs, credentials, and more — including permitted uses, limitation right obligations, and 15-business-day response SLA
- Performs GDPR-to-CCPA/CPRA gap analysis — identifies California-specific additions (Do Not Sell or Share link, GPC, SPI limitation, minors' opt-in, financial incentive disclosures) and structural differences (opt-out vs. opt-in, no lawful basis requirement, breach private right of action)
- Assesses CPPA enforcement and penalty exposure — $2,500/unintentional, $7,500/intentional, $100–$750/consumer for breach class actions — and advises on remediation prioritisation
Potential Use Cases
| Scenario | Relevant Skill(s) |
|---|---|
| Preparing for an ISO 27001:2022 Stage 2 certification audit | ISO 27001 |
| Writing an Information Security Policy mapped to Annex A | ISO 27001 |
| Running a SOC 2 readiness assessment before engaging an auditor | SOC 2 |
| Documenting controls for a SOC 2 Type 2 report | SOC 2 |
| Scoping a FedRAMP Moderate authorization on AWS GovCloud | FedRAMP |
| Writing SSP control narratives for all 20 NIST 800-53 control families | FedRAMP |
| Auditing an API for GDPR compliance before product launch | GDPR |
| Drafting a DPIA for a new AI feature that processes personal data | GDPR |
| Generating a BAA for a healthcare SaaS vendor relationship | HIPAA |
| Assessing whether a data incident constitutes a reportable HIPAA breach | HIPAA |
| Building a compliance program that satisfies both ISO 27001 and SOC 2 | ISO 27001 + SOC 2 |
| Responding to a customer security questionnaire covering multiple frameworks | All skills |
| Assessing current cybersecurity posture using NIST CSF 2.0 | NIST CSF |
| Building a CSF organisational profile with Current and Target states | NIST CSF |
| Scoping a PCI DSS CDE for a cloud-hosted e-commerce platform | PCI DSS |
| Selecting the right SAQ type for a merchant using a hosted payment page | PCI DSS |
| Determining whether your pipeline or rail operation is a TSA covered entity | TSA Cybersecurity |
| Drafting a Cybersecurity Implementation Plan (CIP) for pipeline OT/SCADA environments | TSA Cybersecurity |
| Running an ISO 42001 gap assessment for an AI provider with multiple ML models | ISO 42001 |
| Completing an AI System Impact Assessment (AISIA) for an automated hiring tool | ISO 42001 |
| Integrating an ISO 42001 AIMS with an existing ISO 27001 ISMS | ISO 42001 + ISO 27001 |
| Aligning a TSA CRMP to NIST CSF 2.0 and CISA Cross-Sector CPGs | TSA Cybersecurity + NIST CSF |
| Running an ISO 27701:2025 gap assessment for a SaaS company acting as both PII controller and processor | ISO 27701 |
| Transitioning from ISO 27701:2019 certification to the 2025 standalone edition | ISO 27701 |
| Drafting a GDPR-aligned Data Processing Agreement (DPA) with all required Article 28 clauses | ISO 27701 |
| Completing a DPIA for a new AI feature that profiles users for targeted advertising | ISO 27701 |
| Mapping ISO 27701:2025 controls to GDPR articles for a compliance audit | ISO 27701 |
| Integrating a PIMS with an existing ISO 27001:2022 ISMS to avoid duplicating controls | ISO 27701 + ISO 27001 |
| Running a DORA gap analysis for an EU credit institution ahead of a supervisory review | DORA |
| Classifying an ICT incident against Art. 18 criteria and CDR (EU) 2024/1772 thresholds | DORA |
| Building a three-stage incident reporting procedure (4h / 72h / 1 month) per Art. 19 | DORA |
| Reviewing ICT vendor contracts against Art. 30(2) mandatory provisions | DORA |
| Building or validating the Register of Information per CIR (EU) 2024/2956 | DORA |
| Assessing ICT concentration risk for a bank reliant on a single hyperscaler | DORA |
| Scoping a TLPT programme and evaluating whether Art. 26 applies | DORA |
| Advising on the interaction between DORA and NIS2 for a financial entity | DORA |
| Running a DPDPA gap analysis for an Indian SaaS company ahead of the May 2027 deadline | DPDPA |
| Identifying which GDPR-compliant processing activities need fresh consent under DPDPA | DPDPA + GDPR |
| Designing a Rule 3-compliant notice with multi-language obligations | DPDPA |
| Implementing a 72-hour breach notification pipeline per Section 8(6) and Rule 6 | DPDPA |
| Designing a children's data compliance programme with Rule 12 parental verification | DPDPA |
| Preparing for potential Significant Data Fiduciary designation — DPO, DPIA, audit | DPDPA |
| Updating Data Processing Agreements with vendors to satisfy Rule 16 | DPDPA |
| Assessing India cross-border transfer obligations — blacklist approach and contractual safeguards | DPDPA |
| Determining your CMMC level based on contract DFARS clauses and CUI handling | CMMC 2.0 |
| Running a CMMC Level 2 gap assessment across all 110 NIST SP 800-171 practices | CMMC 2.0 |
| Drafting a System Security Plan (SSP) covering all 110 practices with implementation narratives | CMMC 2.0 |
| Calculating your SPRS score and prioritising the highest-impact gap remediations | CMMC 2.0 |
| Preparing for a C3PAO assessment — evidence packages, critical practices, POA&M rules | CMMC 2.0 |
| Scoping CUI within your organisation and designing an enclave to reduce CMMC scope | CMMC 2.0 |
| Managing DFARS 252.204-7012 72-hour DIBNET incident reporting obligations | CMMC 2.0 |
| Flowing down CMMC requirements to subcontractors handling CUI under DFARS 252.204-7021 | CMMC 2.0 |
| Building an AI organizational profile using NIST AI RMF Current and Target states across all 19 categories | NIST AI RMF |
| Running a GOVERN gap assessment for an organization starting its AI risk programme | NIST AI RMF |
| Evaluating a credit scoring model against MEASURE 2.x trustworthiness criteria before deployment | NIST AI RMF |
| Building an AI risk register mapped to AI RMF categories for a deployed ML system | NIST AI RMF |
| Assessing bias and fairness of a hiring AI tool (demographic parity, equalized odds, EEOC 4/5ths rule) | NIST AI RMF |
| Designing a post-deployment AI monitoring programme using MEASURE 3.x and MANAGE 3.x | NIST AI RMF |
| Mapping NIST AI RMF to the EU AI Act Art. 9 risk management system requirement | NIST AI RMF + ISO 42001 |
| Integrating NIST AI RMF with an existing NIST CSF cybersecurity programme | NIST AI RMF + NIST CSF |
| Determining your SWIFT architecture type (A1/A2/A3/A4/B) and getting the full CSCF v2025 control applicability matrix | SWIFT CSP |
| Running a CSCF v2025 gap assessment for an Alliance Access on-premises deployment | SWIFT CSP |
| Understanding why software OTP fails Control 4.2 and remediating with hardware tokens before the July attestation deadline | SWIFT CSP |
| Preparing evidence and completing the annual KYC-SA attestation via swift.com/myswift | SWIFT CSP |
| Developing a SWIFT-specific incident response plan covering 24-hour notification and 30-day report obligations | SWIFT CSP |
| Verifying your service bureau's (Type B) KYC-SA attestation and understanding split control responsibilities | SWIFT CSP |
| Mapping existing ISO 27001 or PCI DSS controls to CSCF requirements to identify SWIFT-specific gaps | SWIFT CSP + ISO 27001 / PCI DSS |
| Remediating common CSCF non-compliance patterns: shared VLAN, stale patches, missing SIEM coverage, token inventory gaps | SWIFT CSP |
| Understanding which ISM control applicability markings (NC/OS/PROTECTED) apply to an Australian government cloud system and what controls are required | ISM |
| Preparing all artefacts for an IRAP assessment of a PROTECTED-level system — SSP, network diagrams, risk register, control evidence | ISM |
| Hardening a Windows Server 2022 deployment to ISM Chapter 13 requirements with a full evidence checklist | ISM |
| Mapping Essential Eight Maturity Level 2 requirements to their ISM guideline chapters and understanding what ML2 demands for each strategy | ISM |
| Understanding ISM compliance obligations for a private sector cloud provider supplying services to an Australian federal agency | ISM |
| Drafting a System Security Plan (SSP) for ATO sign-off on an OFFICIAL: Sensitive case management system | ISM |
| Understanding approved cryptographic algorithms (AES-256, TLS 1.2+, SHA-256 minimum) and log retention periods under the ISM | ISM |
| Comparing ISM requirements with ISO 27001 controls to identify government-specific gaps not covered by existing certification | ISM + ISO 27001 |
| Determining whether a European energy company is an Essential or Important Entity under NIS2 and understanding its obligations | NIS2 |
| Walking through the NIS2 Art. 23 incident reporting workflow (24h/72h/1-month) after a ransomware attack | NIS2 |
| Performing a gap analysis between an existing ISO 27001:2022 ISMS and full NIS2 compliance | NIS2 + ISO 27001 |
| Drafting an NIS2-compliant incident response policy covering all 10 Art. 21 measures and Art. 23 reporting timelines | NIS2 |
| Explaining the DORA lex specialis relationship and identifying residual NIS2 obligations for a European bank | NIS2 + DORA |
| Understanding Art. 20 management body obligations, personal liability, and required cybersecurity training under NIS2 | NIS2 |
| Assessing supply chain security obligations under NIS2 Art. 21(2)(d) and Art. 26 ENISA coordinated risk assessments | NIS2 |
| Calculating maximum NIS2 penalty exposure and comparing EE vs IE supervisory regimes (Art. 32 vs Art. 33) | NIS2 |
| Determining whether your business meets any CCPA/CPRA threshold ($25M revenue, 100K+ consumers, or 50%+ revenue from PI sale/sharing) | CCPA/CPRA |
| Building a combined right-to-know and right-to-delete response workflow meeting the 45-day deadline | CCPA/CPRA |
| Classifying ad tech activities (cookie sync, RTB, audience segments) as sale vs. sharing vs. service provider processing under CPRA | CCPA/CPRA |
| Identifying and protecting Sensitive Personal Information (SPI) — geolocation, biometrics, health data — with a "Limit the Use of My SPI" mechanism (15-business-day deadline) | CCPA/CPRA |
| Performing a GDPR-to-CCPA/CPRA gap analysis — identifying GPC signal obligation, Do Not Sell or Share link, and SPI limitation rights not required under GDPR | CCPA/CPRA + GDPR |
| Drafting a CCPA-compliant "Do Not Sell or Share My Personal Information" opt-out mechanism that honours Global Privacy Control (GPC) signals | CCPA/CPRA |
| Assessing CPPA enforcement exposure and penalty calculations ($2,500/violation unintentional, $7,500/intentional or for minors' data) | CCPA/CPRA |
| Classifying vendors as service providers, contractors, or third parties under CPRA and updating contracts to include required limitations | CCPA/CPRA |
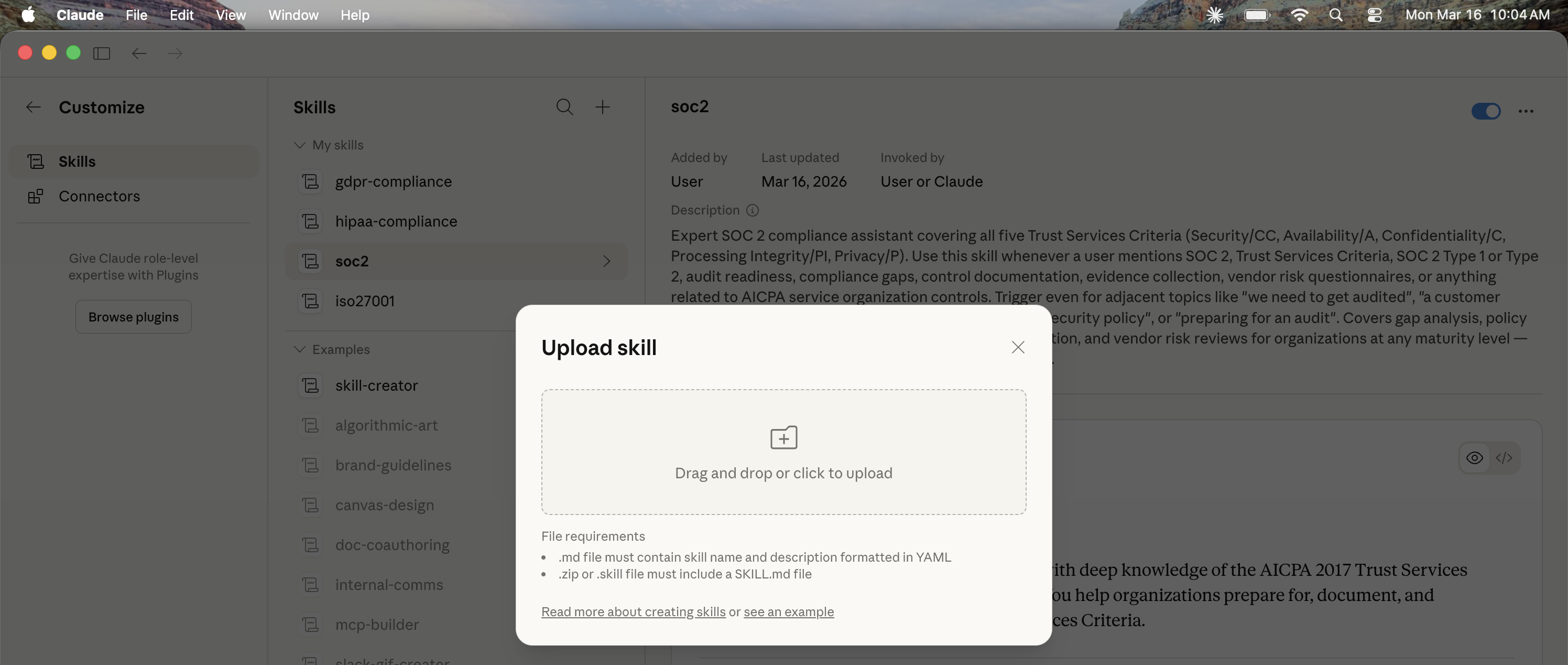
How to Install a Skill
- Download the
.skillfile for the framework you need from the table below. - Open Claude and navigate to Customize → Skills.
- Click Upload Skill and select the
.skillfile. - The skill is now active. Start a new conversation and ask your compliance question — Claude will automatically apply the skill.
| Framework | Download |
|---|---|
| 1. 🔐 ISO 27001 | iso27001.skill |
| 2. ✅ SOC 2 | soc2.skill |
| 3. 🏛️ FedRAMP | fedramp.skill |
| 4. 🇪🇺 GDPR | gdpr-compliance.skill |
| 5. 🏥 HIPAA | hipaa-compliance.skill |
| 6. 🛡️ NIST CSF | NIST Cybersecurity.skill |
| 7. 💳 PCI DSS | PCI-Compliance.skill |
| 8. 🚨 TSA Cybersecurity | TSA-Compliance.skill |
| 9. 🤖 ISO 42001 AI Management System | ISO-42001.skill |
| 10. 🔒 ISO 27701 Privacy Information Management | iso27701.skill |
| 11. 🏦 DORA Digital Operational Resilience | dora.skill |
| 12. 🇮🇳 DPDPA India Digital Personal Data Protection | dpdpa.skill |
| 13. 🛡️ CMMC 2.0 Cybersecurity Maturity Model Certification | cmmc.skill |
| 14. 🤖 NIST AI Risk Management Framework | nist-ai-rmf.skill |
| 15. 🏦 SWIFT Customer Security Programme (CSP) | swift-csp.skill |
| 16. 🇦🇺 Australian Information Security Manual (ISM) | ism.skill |
| 17. 🇪🇺 EU NIS2 Directive | nis2.skill |
| 18. | ccpa.skill |
Install via Claude Code Marketplace
If you use Claude Code — the AI-powered CLI for developers — these skills are also available as installable Claude Code plugins through a hosted marketplace. This is the recommended installation path for developers and teams, as it supports version-pinning, automatic updates, and team-wide distribution without any manual file handling.
Add the marketplace and install the skills you need directly from the terminal:
/plugin marketplace add Sushegaad/Claude-Skills-Governance-Risk-and-Compliance
/plugin install iso27001@grc-skills soc2@grc-skills fedramp@grc-skills gdpr-compliance@grc-skills hipaa-compliance@grc-skills nist-csf@grc-skills pci-compliance@grc-skills tsa-compliance@grc-skills iso42001@grc-skills iso27701@grc-skills dora@grc-skills dpdpa@grc-skills cmmc@grc-skills nist-ai-rmf@grc-skills swift-csp@grc-skills ism@grc-skills nis2@grc-skills ccpa@grc-skillsTeams can pre-wire the marketplace in .claude/settings.json so every developer gets the skills automatically when they open the project — no manual install required.
📖 Full installation instructions, team setup, and update guide → INSTALLATION.md
Skill Evaluation
These skills were benchmarked using the Claude Skill Creator eval framework. 90 realistic test cases were run across all 18 skills — 5 per framework — covering gap analysis, policy drafting, control deep-dives, edge cases, and compliance advice scenarios. Each test case was evaluated against 5 objectively verifiable assertions by independent grader agents comparing skill-assisted vs. baseline Claude responses. 450 total assertions evaluated.
428 / 450 assertions passed
362 / 450 assertions passed
+66 additional assertions passed
Per-Skill Results
| Skill | Cases | With Skill | Baseline | Delta | What Was Tested |
|---|---|---|---|---|---|
| 🔐 ISO 27001 | 5 | 100% | 84% | +16% | Gap assessment; Policy drafting; 2013→2022 transition; Risk assessment; Management review CAP |
| ✅ SOC 2 | 5 | 100% | 84% | +16% | Type 1 vs 2; CC controls checklist; Availability criteria; Access control policy; Audit exception response |
| 🏛️ FedRAMP | 5 | 84% | 76% | +8% | Authorization pathways; Impact levels; FedRAMP 20x; System boundary; POA&M remediation timelines |
| 🇪🇺 GDPR | 5 | 88% | 88% | ±0% | US company checklist; Article 28 DPA; Subject access request; Cookie consent; 72-hour breach notification |
| 🏥 HIPAA | 5 | 92% | 88% | +4% | Covered entity analysis; BAA template; Encryption (addressable vs required); Risk analysis; Workforce violation |
| 🛡️ NIST CSF | 5 | 96% | 84% | +12% | CSF 2.0 overview; Ransomware recovery plan; Profile creation; Control mapping; Board reporting |
| 💳 PCI DSS | 5 | 92% | 88% | +4% | SAQ type selection; Req 3 stored data (v4.0); Breach obligations; Penetration testing; Tokenization scope |
| 🚨 TSA Cybersecurity | 5 | 100% | 96% | +4% | Pipeline directive requirements; CIRP elements; OT/IT segmentation; Airport applicability; TSA vs CIRCIA |
| 🤖 ISO 42001 | 5 | 92% | 80% | +12% | AIMS applicability; Key requirements; AI-specific risks; Third-party LLM management; AI ethics controls |
| 🔏 ISO 27701 | 5 | 100% | 80% | +20% | Extension to ISO 27001; GDPR mapping; Processor controls; PIA methodology; Certification as GDPR evidence |
| 🏦 DORA | 5 | 88% | 72% | +16% | Five pillars; ICT incident reporting timelines; TLPT requirements; Third-party contracts; DORA vs EBA |
| 🇮🇳 DPDPA | 5 | 96% | 80% | +16% | Applicability to foreign entities; Consent vs GDPR; Children's data (18-year threshold); Cross-border transfers; SDF obligations |
| 🛡️ CMMC 2.0 | 5 | 100% | 100% | ±0% | Level determination; SPRS scoring; CUI scoping; SSP structure; C3PAO assessment readiness |
| 🤖 NIST AI RMF | 5 | 92% | 76% | +16% | Four functions overview; Hiring AI risk assessment; Credit scoring risk register; EU AI Act mapping; GOVERN gap assessment |
| 🏦 SWIFT CSP | 5 | 100% | 48% | +52% | Architecture scoping (A1/A2/A3/A4/B); MFA hardware token requirement (Control 4.2); CSCF v2025 gap assessment; KYC-SA attestation process; Incident response obligations (Control 7.1) |
| 🇦🇺 ISM | 5 | 96% | 52% | +44% | OS control scoping and authorisation pathway; IRAP assessment preparation; Chapter 13 system hardening evidence; Essential Eight to ISM chapter mapping; Supply chain cloud provider obligations |
| 🇪🇺 NIS2 | 5 | 96% | 80% | +16% | Energy company EE/IE classification; SaaS provider Art. 21 obligations; Ransomware Art. 23 reporting workflow; ISO 27001 vs NIS2 gap analysis; DORA lex specialis interaction |
| 5 | 100% | 96% | +4% | E-commerce threshold analysis and applicability; Combined right-to-know and delete workflow; Ad tech sale vs sharing classification; GDPR-to-CCPA/CPRA gap analysis; SPI classification for mobile app |
Customer Testimonials
Feedback from the GRC and Claude AI community on LinkedIn, Reddit (r/grc · r/ClaudeAI), and beyond.
"An open-source repository of GRC Claude skills that are pretty good! It has ISO 27001, ISO 42001, SOC 2, FedRAMP, GDPR, and others. I checked them out and tested a few. It looks like the skills are at different levels but definitely a very good starting point if your AI assistant doesn't have any GRC skills installed yet."
"This open-source project by Hemant Naik transforms Claude into a compliance co-pilot using installable 'Skills' covering 9+ major GRC frameworks. The benchmark shows a 94% pass rate vs 72% for baseline Claude — a solid +22 point lift, especially on accurate citations. Practical for audit preparation, gap assessments, control mapping, and policy drafting. This represents genuine progress toward interactive, intelligence-driven compliance."
"Fantastic work. Going to follow this and test it out myself."
"This is awesome, thank you!"
"This is awesome! Any chance you can build one for ISO 42001?"
"As a rather new Claude Code user, I'm both impressed and thankful. It's really helpful that you release it publicly. I am at the stage where I understand the need for a well-written CLAUDE.md and skills. This will help me a lot."
"The skills approach is a good entry point — getting Claude to reason about specific frameworks is exactly the right instinct. The gap I kept hitting was that Claude could describe the compliance picture but couldn't act on it... this is a great start."
"I've been doing something similar for the CIS controls and it's been brilliant so far. I'll be using this for ISO and SOC 2. Thanks!"
"Hell ya. We just approved Claude for enterprise so I'll go check it out."
"I'll definitely check this out. I have a skill for threat modeling and am working on some other ones, this is super helpful."
"Awesome, thanks for sharing. I'm going to play around with this."
Share Your Feedback
Have you used the GRC Claude Skills? We'd love to hear what you think — your feedback helps improve future skills and guides new framework coverage.
GRC Framework Updates
This section tracks official regulatory and standards activity across the 15 frameworks covered in this repository. Updated monthly to help GRC practitioners stay ahead of changes — new versions, enforcement actions, guidance releases, and compliance deadline shifts. Each entry below covers April 2026 only; prior months are archived in collapsible sections below.
🗓️ April 2026 Current
Published: April 26, 2026
ISO 27001
The October 2025 transition deadline has passed — all ISO 27001 certifications must now be to the ISO/IEC 27001:2022 edition. Certificates still referencing the 2013 standard are no longer valid. The earlier Amendment 1:2024 (climate action changes) remains in effect, requiring organisations to consider climate-related factors when scoping their ISMS. No new version is expected before 2027.
SOC 2
The AICPA's 2017 Trust Services Criteria remain unchanged. In early 2026, the AICPA issued revised points of focus clarifying how controls address evolving technologies — with greater emphasis on MFA, network segmentation, least-privilege access, and API security. Auditors are now treating these as standard evidence expectations in Type II engagements, even where not previously enforced.
HIPAA
Two significant changes took effect or are imminent. First, as of February 16, 2026, covered entities must include substance use disorder (SUD) record information in their Notice of Privacy Practices — a new Part 2 rule requirement. Second, the long-awaited HIPAA Security Rule overhaul is expected to be finalised by May 2026, eliminating the "addressable" vs "required" safeguard distinction and making MFA, encryption-at-rest, and network segmentation universally mandatory.
GDPR
The EDPB launched its Coordinated Enforcement Framework (CEF) 2026, targeting transparency and information obligations — national authorities across the EU are running aligned audits on how clearly organisations explain data processing. Two major enforcement actions remain active: Ireland's DPC fined LinkedIn €310 million and X Corp €550 million for unlawful data processing for ad targeting. Cumulative GDPR fines have now exceeded €7.1 billion across 2,245+ documented cases.
FedRAMP
April 8, 2026: RFC-0031 Updated Incident Communications Procedures was published, refining how CSPs evaluate and escalate incidents affecting federal customer data. Separately, FedRAMP Ready status is being retired on July 28, 2026, replaced by a Rev5 Class A (Pilot) designation. The Consolidated Rules 2026 (CR26) enforcement window begins January 2027, requiring migration away from the connect.gov portal, which will be retired at that time.
NIST CSF
NIST released two new CSF 2.0 Quick-Start Guides in April 2026. The final SP 1308 (Cybersecurity, ERM, and Workforce Management QSG) is now available, helping organisations integrate cybersecurity risk with enterprise risk management and HR planning. Additionally, the Initial Public Draft of SP 1347 (Informative References QSG) is out for a 45-day public comment period closing May 6, 2026.
PCI DSS
PCI DSS v4.0.1 is now the sole active version following the retirement of v4.0 in December 2024 and v3.2.1 in March 2024. All 64 future-dated requirements from v4.x became mandatory on March 31, 2025. In 2026, organisations are completing their first full-cycle assessments under v4.0.1, which include stricter requirements for e-commerce script security (Req. 6.4.3), targeted risk analyses (Req. 12.3.2), and expanded cryptographic controls. No v4.1 announcement has been made.
ISO 27701
ISO/IEC 27701 was substantially updated in October 2025, becoming a fully standalone standard — organisations no longer require ISO 27001 certification as a prerequisite. April 2026 marks a key milestone: accreditation bodies (including UKAS) are now ready to assess against ISO 27701:2025, with formal certification body assessments commencing from May 2026. The full transition deadline for existing 2019 certifications is October 2028.
ISO 42001
No revision to ISO/IEC 42001:2023 is expected in 2026 — the standard remains at its initial release. Adoption is accelerating: the Cloud Security Alliance published updated FAQs in February 2026 addressing how ISO 42001 integrates with ISO 27001 and ISO 27701 for organisations building unified governance frameworks. AI system impact assessments (a core prerequisite to risk assessment under the standard) are receiving increased scrutiny from early certification auditors.
DORA
DORA has been fully in force since January 17, 2025. In 2026, the European Supervisory Authorities (ESAs) are advancing the designation of Critical Third-Party ICT Providers (CTPPs) — the first formal CTPP oversight engagements are underway this year. Financial entities are now operating full ICT incident reporting cycles (4h initial / 72h intermediate / 1 month final report) and submitting ICT third-party registers to national competent authorities. No amendments to the regulation are pending.
DPDPA (India)
India's DPDP Rules 2025 were finalised on November 13, 2025. Implementation is phased: Phase II obligations (consent manager provisions) take effect in November 2026, while substantive compliance obligations for all Data Fiduciaries become enforceable in May 2027. In 2026, the government is expected to designate the first cohort of Significant Data Fiduciaries (SDFs), which will trigger stricter obligations including DPIA requirements and data localisation duties.
TSA Cybersecurity
TSA renewed its pipeline security directives in early 2026. SD Pipeline-2021-01G (issued January 9, 2026) is the latest revision of the incident reporting and cybersecurity coordinator requirements for pipeline operators. The freight rail directive SD 1580-21-01E (effective January 16, 2026 through January 15, 2027) continues to require freight railroad operators to maintain Cyber Risk Management Programs. TSA is also advancing a proposed rulemaking to formalise these directives as permanent regulation.
CMMC 2.0
CMMC is in active Phase 1 enforcement (since November 10, 2025): DoD contracts now require CMMC Level 1 or Level 2 self-assessments as a condition of award. Phase 2 begins November 10, 2026, at which point official C3PAO third-party assessments for Level 2 contractors become mandatory. By October 31, 2026, CMMC compliance will be required for all new DoD contract awards. Contractors should be submitting their SPRS scores and completing any outstanding POA&Ms now.
NIST AI RMF
NIST published a new AI RMF Profile for Trustworthy AI in Critical Infrastructure on April 7, 2026 (concept note stage), covering Energy, Water, Healthcare, and Financial Services. In February 2026, NIST released the preliminary draft of the Cybersecurity Framework Profile for AI (NIST IR 8596), which extends CSF 2.0 to AI-specific cybersecurity risks. The February-launched AI Agent Standards Initiative introduces a three-pillar programme (security, interoperability, identity) for autonomous AI systems. AI RMF 1.1 addenda are expected later in 2026.
SWIFT CSP
CSCF v2026 is now the active framework for the current attestation cycle. The most impactful change: Control 2.4 moves from advisory to mandatory, requiring all institutions to formally identify and prioritise data flows between the SWIFT secure zone and back-office systems. v2026 also introduces minimum key size and cipher requirements (TLS 1.2+, SSH2 mandatory), formalises AI-related risk considerations, and adds cloud shared-responsibility model visuals to Appendix G. The annual KYC-SA attestation deadline remains July 31, 2026.
📁 Older Updates
No prior monthly updates yet. This section will collect previous months as new editions are published.
Support
Reporting Issues
If you find an error, outdated regulatory reference, or missing coverage in any skill, please open a GitHub issue and include:
- The skill name (e.g., ISO 27001, FedRAMP)
- A description of the issue or incorrect guidance
- The correct information with a source reference if possible (e.g., regulatory text, official guidance document)
Requesting New Skills
Have a compliance framework not covered here? Open a GitHub issue with the tag skill-request and describe the framework, your use case, and the audience it would serve. Community suggestions are welcome for frameworks such as CMMC, CCPA, SOX, and others.
Author
Hemant Naik
LinkedIn · hemant.naik@gmail.com
Built March 2026
Disclaimer
The skills in this repository provide informational guidance based on publicly available regulatory and standards documentation. They do not constitute legal, audit, or professional compliance advice. Outputs should be reviewed by qualified professionals — such as a certified ISO 27001 Lead Auditor, licensed attorney, Data Protection Officer, or HIPAA compliance officer — before being relied upon for formal compliance purposes.
Regulatory requirements evolve. Always verify guidance against the latest official publications from the relevant standards body or regulatory authority.
Licensed under the MIT License.
Release Notes
Full changelog for all public releases. Latest release: v0.7.0.
🆕 New Skills (3)
- New Australian Information Security Manual (ISM) — Expert advisor for the ASD Information Security Manual; covers control applicability markings (NC/OS/PROTECTED), system authorisation and IRAP assessment preparation, Essential Eight Maturity Level mapping to ISM chapters, Chapter 13 system hardening, supply chain obligations for private sector cloud providers, and government-specific gaps not covered by ISO 27001 certification
- New EU NIS2 Directive — Expert advisor for the NIS2 Directive (Directive (EU) 2022/2555); covers Essential vs Important Entity classification (Annex I/II), all 10 Art. 21 security measures, Art. 23 incident reporting timelines (24h/72h/1 month), Art. 20 management body accountability, supply chain security under Art. 21(2)(d) and Art. 26 ENISA assessments, ISO 27001 gap analysis, and DORA lex specialis interaction for financial entities
- New CCPA/CPRA California Privacy — Expert advisor for the California Consumer Privacy Act (CCPA) and California Privacy Rights Act (CPRA/Proposition 24); covers business threshold analysis, all 7 consumer rights with deadlines (45-day standard, 15-business-day for SPI), Sensitive Personal Information (SPI) classification and limitation mechanisms, Do Not Sell or Share link, Global Privacy Control (GPC) signal obligations, ad tech sale vs. sharing classification, service provider/contractor/third-party classification, CPPA enforcement and penalty exposure ($2,500/$7,500 per violation), and GDPR-to-CCPA/CPRA gap analysis
📊 Eval Suite Expansion
- New Expanded from 75 → 90 test cases and 375 → 450 assertions — 5 ISM evals (control scoping and authorisation, IRAP preparation, Chapter 13 hardening, Essential Eight mapping, supply chain obligations), 5 NIS2 evals (entity classification, Art. 21 obligations, Art. 23 reporting, ISO 27001 gap, DORA interaction), and 5 CCPA/CPRA evals (threshold analysis, right-to-know/delete workflow, ad tech classification, GDPR gap analysis, SPI classification)
- Improved Updated benchmark: 95% with-skill (428/450) / 80% baseline (362/450) / +66 additional assertions passing
🌐 GitHub Pages — Improvements
- Improved Header updated — title changed to "Claude Skills for Governance, Risk, & Compliance Frameworks"; skills grid fixed to 6 columns for even rows (18 items ÷ 6 = 3 equal rows)
- Improved CCPA/CPRA uses the actual California flag — replaced unreliable subdivision tag emoji with the Wikimedia Commons California state flag SVG, rendered inline at text size
🆕 New Skills (3)
- New CMMC 2.0 Cybersecurity Maturity Model Certification — Expert advisor for DoD contractors; covers all three CMMC levels (Foundational, Advanced, Expert), 110 NIST SP 800-171 practices, CMMC Level 2 self-assessment vs. C3PAO third-party assessment, POA&M eligibility, SPRS scoring, and OSC/OSA/C3PAO role guidance
- New NIST AI RMF AI Risk Management Framework — Full coverage of NIST AI RMF 1.0 and AI RMF Playbook; all four core functions (GOVERN, MAP, MEASURE, MANAGE), AI risk taxonomy (bias, explainability, security, privacy, safety), trustworthy AI characteristics, tiered risk profiles, and sector-specific guidance
- New SWIFT CSP Customer Security Programme — Expert CSCF v2025 advisor for SWIFT member institutions; all 31 controls (23 mandatory + 8 advisory), all architecture types (A1/A2/A3/A4/B), KYC-SA attestation workflow, hardware MFA token requirements, critical patch SLA, and incident response obligations under Control 7.1
📊 Eval Suite Expansion
- New Expanded from 70 → 75 test cases and 350 → 375 assertions — 5 new SWIFT CSP evals covering architecture scoping, MFA hardware tokens, gap assessment, KYC-SA attestation, and incident response
- Improved Updated benchmark: 95% with-skill / 81% baseline / +14 pts delta / +50 additional assertions passing vs. baseline
🌐 GitHub Pages — UX Improvements
- Improved Skills header redesigned — replaced run-on 15-framework sentence with a clean responsive grid (5 cols → 3 cols → 2 cols) for better readability at all screen sizes
- Fix Skill cards sorted by number — CMMC #13, NIST AI RMF #14, and SWIFT CSP #15 now display in correct order (CMMC was previously appearing last)
- New Added second LinkedIn testimonial — Shubham Mishra, Security Engineering @ Juniper Networks: "genuine progress toward interactive, intelligence-driven compliance"
🌐 GitHub Pages — Site Improvements
- New Added dedicated 📋 Release Notes tab — moved out of Resources for easier access
- New Added LinkedIn testimonial card (Jaana Metsamaa, Co-Founder at Kontion.app) with screenshot and link to post — featured above the Reddit testimonials grid
- New Added GitHub Stars live badge to the site header and README
- Improved Meta description updated to include all 12 skills
📊 Eval Results Page — Rebuilt
- Fix Eval results page previously only showed 36 runs (9 skills). Rebuilt to correctly display all 120 runs (60 prompts × 2 configs) across all 12 skills with accurate benchmark stats (94% / 83% / +11% / +32 assertions)
- Improved Results table links now open and scroll to the corresponding skill accordion
🐛 Bug Fixes — Skill Installability
- Fix DORA and DPDPA skills failed to install with "field 'description' in SKILL.md must be at most 1024 characters" — descriptions trimmed to ~875–890 chars while preserving all key triggering terms
- Fix DORA, DPDPA, ISO 27701, ISO 42001, and FedRAMP plugin
.skillZIPs had an extraskills/wrapper, causing "SKILL.md must be in the top-level folder" install errors. All five rebuilt with correct<name>/SKILL.mdstructure
🆕 New Skills (3)
- New ISO 27701 Privacy Information Management — Expert PIMS advisor covering both ISO 27701:2025 (standalone) and ISO 27701:2019 (ISO 27001 extension); gap analysis, SoA generation, privacy risk assessment, DPIA support, and GDPR/CCPA/LGPD alignment across all 78 Annex A controls (A.1 controller, A.2 processor, A.3 shared security)
- New DORA Digital Operational Resilience — Full DORA (Regulation (EU) 2022/2554) compliance advisor for EU financial entities; covers all 64 articles, all 12 adopted RTS/ITS, ICT risk management framework, incident classification and three-stage reporting (4h/72h/1 month), TLPT scoping, ICT third-party risk, and Register of Information requirements
- New DPDPA India Digital Personal Data Protection — Advisor covering India's Digital Personal Data Protection Act, 2023 and DPDP Rules, 2025 (effective May 2027); all 44 sections and 23 Rules, notice and consent requirements, Data Principal rights, 72-hour breach notification, children's data (18-year threshold), Significant Data Fiduciary obligations, and GDPR-to-DPDPA gap analysis
🏛️ FedRAMP Skill — Improvements
- Improved Updated based on user feedback
🤖 ISO 42001 Skill — Improvements
- Improved Updated based on user feedback
🔒 ISO 27701 Skill — Improvements
- Improved Rewrote version-selection logic: skill now leads with the 2019 extension model when the user has an existing ISO 27001 certification, and defaults to the 2025 standalone edition for greenfield implementations — previously defaulted to 2025 in all cases
- Improved GDPR alignment is now mentioned in the opening paragraph of every ISO 27701 explanation — the standard's primary value proposition was previously buried in a reference table
- New Added PII Processor terminology table with exact ISO 27701 control language ("PII subject rights assistance obligations", "sub-processor notification and consent", "processing under controller authority") — these are the precise phrases used in audits and DPA contracts
- New Added explicit "Key Statements" section covering: ISO 27701 is not a GDPR safe harbor; it has not been approved as a formal Article 42 GDPR certification scheme; ISO 27701:2019 requires ISO 27001 as a prerequisite and cannot be certified standalone
🐛 Fix — ISO 27701 Standalone Skill File
- Fix The
ISO 27701 - Claude Skill/iso27701.skillZIP was missing entirely — the directory existed but contained no installable file. The standalone skill archive has been built and published.
📊 Skill Evaluation — Updated Benchmark
- Improved Re-ran the 60-case eval suite following ISO 27701 skill improvements. ISO 27701 delta flipped from −8% to +20% (76% → 100% with skill)
- Improved Overall suite: skills now score 94% vs baseline of 83% (+11 point delta, 282/300 assertions passed), up from 92% / +8pts in v0.3.0
🌐 GitHub Pages — Multi-Tab Site
- New Replaced the Jekyll/README default page with a fully custom, multi-tab
index.htmlcovering Skills, Installation, Evaluation, Customer Feedback, and Resources - New Embedded YouTube demo video directly in the Skills tab
- New Interactive Customer Feedback tab with Formspree-powered contact form (Customer Name, Company, Feedback Title, Feedback Body) — submissions delivered to hemant.naik@gmail.com
- New Integrated Formspree Ajax library (
@formspree/ajax) via CDN for inline field validation and no-reload submissions - New Release Notes section (this section) added to the Resources tab
- Improved Evaluation tab now shows stat cards (92% / 84% / +8pts) and per-skill results table for all 12 skills
🐛 Bug Fixes — Skill Installability
- Fix NIST CSF, PCI DSS, TSA Cybersecurity, and ISO 42001
.skillfiles were failing to install with the error "SKILL.md file must be in the top-level folder, not nested deeper" — caused bySKILL.mdbeing packaged two levels deep (skills/<name>/SKILL.md) instead of one (<name>/SKILL.md). All four skills have been repackaged correctly.
🧪 Test Suite
- New Added
tests/test_skill_installability.py— validates ZIP structure, SKILL.md depth, path safety, and content for all 9.skillfiles (169 assertions, runs withpytest) - New Added
tests/test_plugin_structure.py— validates plugin directory layout,plugin.jsonschema, semver versioning, andmarketplace.jsoncompleteness for all 9 plugins
🆕 New Skills (4)
- New NIST CSF — CSF 2.0 and CSF 1.1 advisor covering all six functions (Govern, Identify, Protect, Detect, Respond, Recover), gap assessments, organisational profiles, and implementation tiers
- New PCI DSS — PCI DSS v4.0.1 advisor covering all 12 requirements, all 8 SAQ types, CDE scoping, v3.2.1 → v4.0.1 migration guidance
- New TSA Cybersecurity — TSA Security Directive advisor for pipeline and rail critical infrastructure, CRMP drafting, OT/ICS implementation, and CISA 24-hour incident reporting
- New ISO 42001 AI Management System — ISO/IEC 42001:2023 AIMS advisor covering all 38 Annex A controls (A.2–A.10), AISIA methodology, AI risk assessment, and EU AI Act mapping
📊 Skill Evaluation
- Improved Expanded eval suite to 12 skills / 60 test cases (5 per framework), each graded against 5 verifiable assertions by independent grader agents — 300 total assertions
- Improved Skills scored 92% vs baseline of 84% (+8 point improvement, +24 additional assertions passed)
- Improved Evaluation tab updated with full 60-case results for all 12 skills including DORA and DPDPA
🐛 Bug Fixes
- Fix Resolved Issue #8 — Claude Code plugin loader path doubling bug where
marketplace.jsonentries with explicitskillsarrays caused the installer to construct double-nested paths, preventing plugin loading. Version bump forces cache invalidation for affected users.
📖 Documentation
- New Customer Testimonials section added to README with 9 community responses from Reddit
- Improved README Skill Evaluation section rewritten with new benchmark summary table and per-skill results
- New YouTube demo video embedded in README and GitHub Pages site
🚀 Initial Release
- New ISO 27001 — gap analysis, policy drafting, risk registers, SoA templates; covers ISO 27001:2013 and ISO 27001:2022
- New SOC 2 — Trust Services Criteria coverage (CC, A, C, PI, P), control documentation, vendor risk questionnaires, Type 1 / Type 2 guidance
- New FedRAMP — ATO lifecycle advisor, SSP and POA&M authoring, NIST 800-53 Rev 5, cloud architecture guidance for AWS GovCloud / Azure Government / GCP
- New GDPR — code and architecture audits, Privacy Notices, DPAs, DPIAs, data subject rights, UK GDPR notes
- New HIPAA — Privacy Rule, Security Rule, Breach Notification Rule; BAA and NPP templates; technical safeguards for cloud environments
- New Claude Code plugin marketplace integration — all 5 skills available via
/plugin install - New Skill eval framework with 10 baseline test cases across the 5 initial skills




